Access Control Solutions
1. Network Access Control (NAC)
Definition:
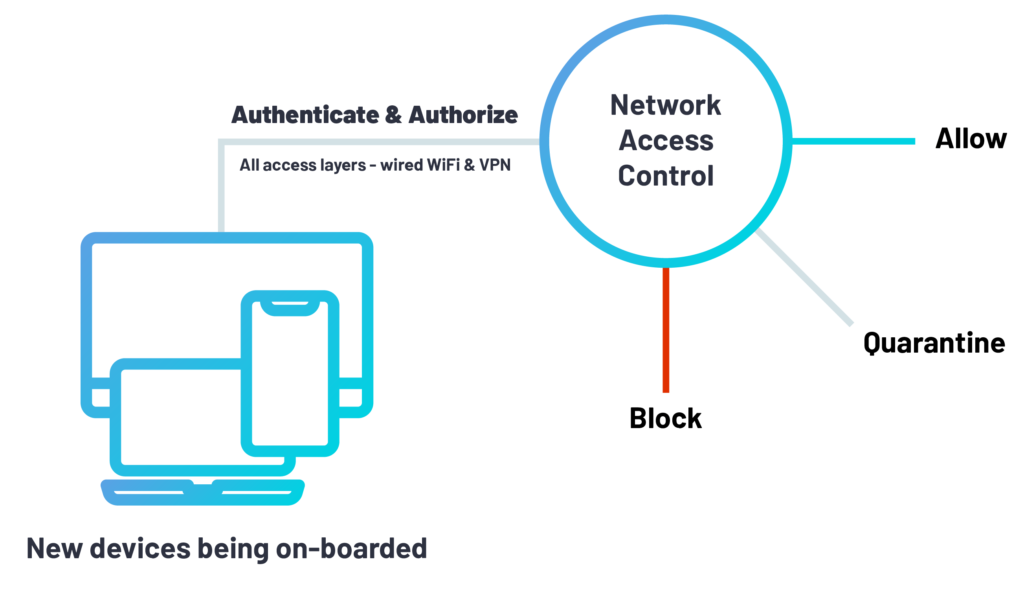
NAC is a security solution that enforces policies on devices trying to access a network. It ensures that only authenticated and compliant devices (and users) can access network resources. Essentially, it acts as a gatekeeper for your network.
Key Goals of NAC:
Authentication: Verify that users and devices are who they claim to be.
Authorization: Control what network resources they can access based on policies.
Compliance Enforcement: Check if devices meet security requirements (e.g., antivirus updated, OS patched).
Visibility: Identify all devices connected to the network, including IoT or BYOD devices.
How NAC works:
A device tries to connect to the network.
NAC checks the device’s identity (via credentials, certificates, or network authentication).
NAC evaluates device compliance (security posture).
If the device meets policy, it’s granted access; otherwise, access is restricted or quarantined.
Examples of NAC solutions: Cisco ISE, Aruba ClearPass.
2. Arcon
Definition:
Arcon is a privileged access management (PAM) solution that controls and monitors privileged users’ access to critical systems.
Relation to NAC:
NAC ensures devices and users can access the network, but Arcon focuses on controlling what privileged users can do once inside.
It limits access to sensitive systems based on user roles, enforces session monitoring, and logs activities for auditing.
Key Features:
Role-based access for privileged accounts.
Session recording and monitoring.
Password vaulting and management.
Compliance reporting.
Example Use Case:
An IT admin tries to access a database server. Arcon ensures only authorized admins can log in, records the session, and restricts certain commands.
3. Data Classification Services
Definition:
Data Classification Services label and categorize data based on sensitivity, compliance, or confidentiality levels (e.g., Public, Internal, Confidential, Highly Confidential).
Relation to NAC:
NAC can use data classification labels to enforce access policies. For instance:
Devices/users accessing highly confidential data must meet stricter compliance checks.
Restricted data may only be accessible from managed devices or secure network zones.
Key Benefits:
Helps in enforcing access policies more granularly.
Supports regulatory compliance (GDPR, HIPAA, etc.).
Reduces the risk of data leakage.
4. Identity and Access Management (IAM)
Definition:
IAM is a framework that manages digital identities and their access to resources. It ensures the right users have the right access at the right time.
Relation to NAC:
NAC authenticates devices and users on the network, while IAM manages identity verification, roles, and permissions across systems.
IAM integrates with NAC to enforce policies based on user identity and role.
Key IAM Functions:
User provisioning and deprovisioning.
Role-based access control (RBAC).
Single sign-on (SSO) and multi-factor authentication (MFA).
Access audits and compliance reporting.
Example:
A marketing employee can access marketing servers but not financial data. IAM defines this role-based access.