Network Detection and Response (NDR)
Introduction to Network Detection and Response (NDR)
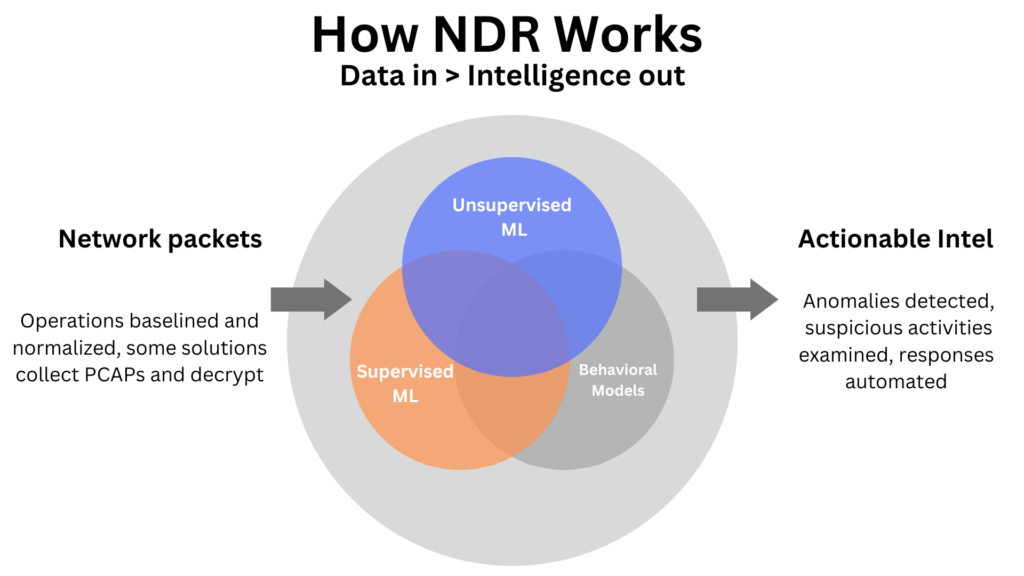
Network Detection and Response (NDR) tools are, in essence, cybersecurity solutions that primarily focus on detecting threats, monitoring network traffic, and responding to cyberattacks at the network level. Moreover, these tools are specifically designed to identify unusual or suspicious behavior within organizational networks. Consequently, they provide advanced analysis capabilities, which help uncover complex threats that might otherwise go unnoticed by traditional security tools.
Why NDR is Essential
Firstly, NDR tools reduce threat detection time because they continuously analyze network traffic using advanced techniques. As a result, organizations can identify potential threats much faster.
Additionally, by leveraging sophisticated algorithms, NDRs increase detection accuracy, which in turn reduces false alarms and enhances responsiveness.
Furthermore, many NDR systems come equipped with automated response capabilities; thus, they can act immediately to contain and mitigate threats.
Finally, NDRs provide comprehensive network visibility, allowing security managers to make well-informed decisions and strengthen overall security posture.
Key Use Cases of NDR
1. Network Traffic Analysis
NDR tools analyze network traffic to detect unusual or anomalous patterns that may indicate malicious activity. Furthermore, they help identify attacks that might bypass traditional security measures, such as advanced persistent threats (APTs).
2. Detection of Advanced Threats
By using machine learning and complex algorithms, NDRs can detect threats that other security tools often overlook. Therefore, organizations gain the advantage of identifying sophisticated attacks early.
3. Immediate Threat Response
After detecting a threat, NDR tools can take immediate action to prevent further damage. For example, they may isolate infected devices, block suspicious traffic, or execute remediation scripts. Consequently, potential breaches are contained before they escalate.
4. Comprehensive Network Visibility
NDRs provide administrators with a broad, real-time view of network activity. As a result, organizations can strengthen defenses, refine security policies, and assess overall network health more effectively.
5. Reducing False Positives
Moreover, advanced analytics help distinguish between normal and malicious activity, thereby reducing false alarms that might otherwise consume security team resources unnecessarily.
Leading NDR Platforms
Several NDR platforms are widely recognized for their capabilities. For instance:
Darktrace – Automatically models normal network behavior and detects deviations in real time using AI.
Vectra AI – Focuses on analyzing network behavior through sophisticated algorithms to detect evolving attacks.
Cisco Stealthwatch – Provides extensive traffic analysis, identifies a variety of threats, and offers comprehensive network visibility.
ExtraHop Reveal(x) – Concentrates on identifying and responding to network-based threats and anomalous behavior.
Palo Alto Networks Cortex – Integrates network analytics for automated detection and response to threats.
Therefore, these platforms enable organizations to manage threats efficiently, using advanced analytics and rapid response to protect critical digital assets.
Key Features of NDR
Advanced Network Traffic Analysis
NDRs employ AI, machine learning, and behavioral analysis to detect suspicious traffic patterns.
Comprehensive Threat Detection
They identify stealthy intrusions, malware, and other malicious activities that conventional antivirus or firewalls might miss.
Automated Response
Following threat detection, NDR tools can isolate devices, block malicious traffic, or alert security managers, thereby containing the threat immediately.
Complete Network Visibility
By providing a complete view of network activity, NDRs allow security managers to monitor, analyze, and strengthen network defenses continuously.
NDR vs. EDR: Understanding the Difference
| Aspect | EDR (Endpoint Detection & Response) | NDR (Network Detection & Response) |
|---|---|---|
| Primary Focus | Endpoint devices such as computers, laptops, and servers | Network traffic and overall network activity |
| Threat Detection | Detects malware and attacks based on endpoint behavior using AI | Detects hidden or complex attacks through network traffic patterns |
| Response Mechanism | Endpoint-level actions, including quarantining files or terminating malicious processes | Network-level actions, such as isolating suspicious devices or blocking threat traffic |
| Analysis Capabilities | In-depth endpoint analysis (files, processes, registries) | Broad network-wide analysis across multiple devices |
Consequently, while both EDR and NDR are essential for cybersecurity, they complement each other perfectly. Hence, using both provides layered protection against a wide range of threats.
Conclusion
In conclusion, leveraging both NDR and EDR creates a robust, multi-layered defense. As a result, organizations can ensure comprehensive protection of their networks and digital assets against increasingly sophisticated cyber threats. Therefore, integrating these solutions is critical for maintaining a strong cybersecurity posture.