Penetration Test and Vulnerability Assessment
Penetration Testing vs Vulnerability Assessment in Networking: Complete Guide
Introduction to Network Security
In today’s digital world, network security is critical. Organizations face constant threats from hackers and cybercriminals. To protect networks, two key processes are used: Vulnerability Assessment (VA) and Penetration Testing (PT). Both help organizations identify security weaknesses, but they serve different purposes and provide unique insights into cyber risks.
What is a Vulnerability Assessment (VA)?
Definition
A Vulnerability Assessment is a systematic, automated process that scans your network to find security gaps, misconfigurations, and weaknesses before attackers exploit them.
Purpose
The goal of VA is to identify vulnerabilities, evaluate risk levels, and prioritize fixes. It’s proactive, helping businesses prevent attacks before they happen.
Key Features
- Wide Coverage: Scans all devices, servers, applications, and network services.
- Non-Intrusive: Identifies weaknesses without exploiting them.
- Automated Tools: Uses scanners like Nessus, Qualys, and OpenVAS.
- Risk Classification: Prioritizes vulnerabilities as Low, Medium, High, or Critical.
- Regular Checks: Often performed on a routine basis for ongoing security.
Output
A VA report includes:
- A detailed list of vulnerabilities
- Severity ratings for each issue
- Affected devices or services
- Recommendations to fix issues
What is Penetration Testing (PT)?
Definition
Penetration Testing is a controlled, ethical hacking process where cybersecurity experts attempt to exploit network vulnerabilities to measure real-world attack impact.
Purpose
The goal of PT is to simulate an attacker’s tactics, understand how far an intruder can penetrate, and test the effectiveness of security controls.
Key Features
- Intrusive Testing: Exploits vulnerabilities to reveal real threats.
- Hybrid Approach: Combines manual testing with automated tools.
- Adversary Simulation: Mimics hacker behavior to assess risk.
- Scenario-Based: Focuses on critical systems and potential attack paths.
- Deep Analysis: Provides insight into potential damage if attacked.
Output
A PT report contains:
- Successfully exploited vulnerabilities
- Attack pathways and proof of compromise
- Security weaknesses and control failures
- Recommendations for hardening defenses
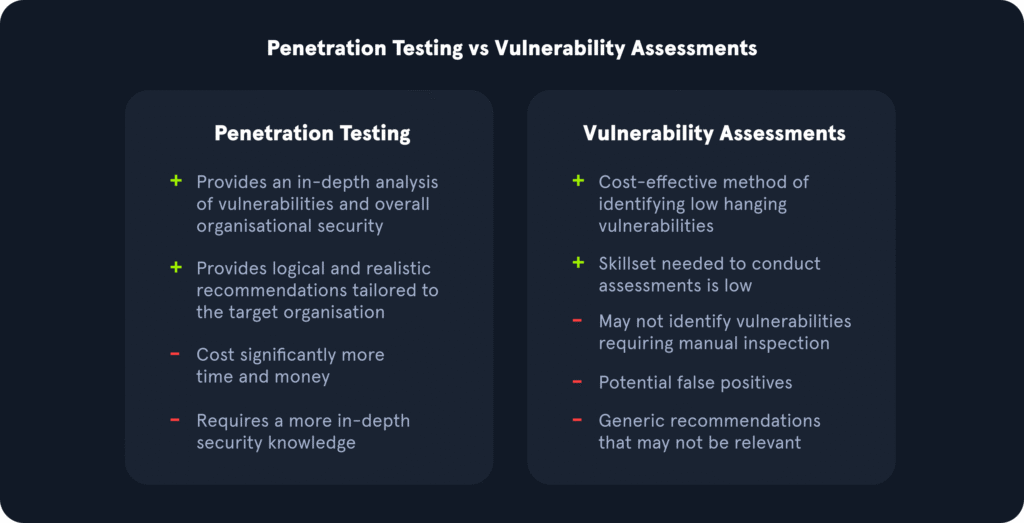
Vulnerability Assessment vs Penetration Testing
Feature | Vulnerability Assessment | Penetration Testing |
Purpose | Detect potential weaknesses | Exploit vulnerabilities to test impact |
Method | Automated scanning | Manual + automated attacks |
Depth | Broad and shallow | Narrow and deep |
Risk Demonstration | Theoretical | Practical, proof-based |
Intrusiveness | Non-intrusive | Intrusive |
Frequency | Regular/continuous | Periodic/strategic |
Why Both Are Important
Using both VA and PT gives your organization a comprehensive security strategy:
- Detects weaknesses before hackers do
- Tests real-world attack scenarios
- Strengthens security controls and defenses
- Reduces risk of breaches
- Improves incident response
Conclusion
Vulnerability Assessment shows what could go wrong, while Penetration Testing demonstrates what will go wrong if not fixed. Together, they provide powerful, actionable insights that protect your network from evolving cyber threats.