Extended Detection and Response (XDR)
Cybersecurity on the Edge: Why XDR Matters Now More Than Ever
In today’s hyper-connected, fast-moving digital world, organizational networks are more complex and vulnerable than ever. Cyber threats are growing faster than ever, with Advanced Persistent Threats (APTs) targeting governments, enterprises, and critical systems. Traditional security methods just aren’t enough anymore, especially as attackers are now using AI tools like ChatGPT to create clever, sophisticated zero-day attacks.
The good news? AI-powered, intelligent security platforms like XDR are here to help. They can spot, intercept, and stop threats in their tracks, protecting users, applications, and networks in real time.
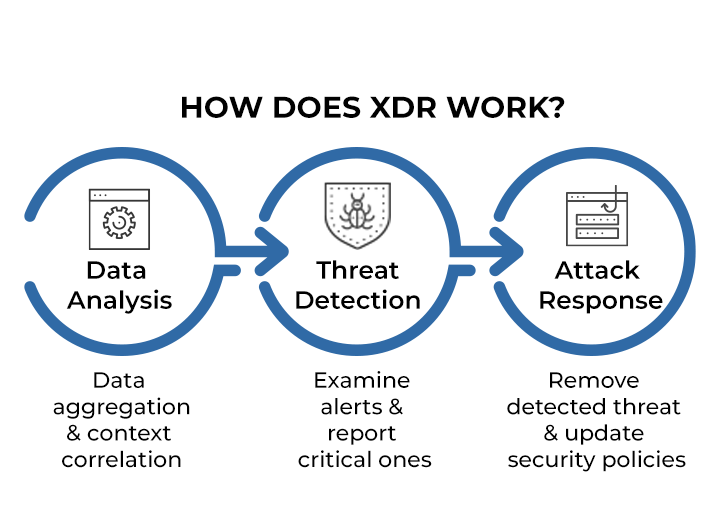
Extended Detection and Response (XDR) is the next level of cybersecurity, going beyond old-school EDR. By combining smart analytics, automation, and fast response, XDR keeps your organization protected from even the trickiest, most complex attacks.
The Threat Landscape: Why You Can’t Wait
APTs are planned, multi-stage attacks that unfold over time. They take advantage of zero-day vulnerabilities and use sophisticated malware to go after critical data and systems.
To fight back, you need machine learning-powered XDR. It continuously collects and analyzes data from servers, clients, and network traffic. By spotting unusual behavior early and simulating how attacks might unfold, XDR can stop threats before they cause real damage.
What Makes XDR So Powerful
- Always-On Monitoring and Smart Analysis
XDR keeps an eye on everything—endpoints, networks, servers, and cloud environments. It sorts through thousands of alerts to highlight only the most critical issues, so your team can act quickly.
- Spotting Threats Before They Spread
With complete visibility, XDR can detect attacks hiding in software, ports, and protocols. It traces the source, stops lateral movement, and keeps your network safe.
- Fast, Effective Response
Unlike traditional EDR that only acts at endpoints, XDR can respond across your whole IT environment. Policies are updated dynamically to neutralize threats and prevent repeat attacks.
Top XDR Solutions to Consider
- Trend Micro
- Kaspersky KATA
- Microsoft
- Sangfor
Key Features That Make XDR Stand Out
- Proactive Threat Hunting: Automatically searches for hidden threats, letting your team focus on strategic tasks.
- Smart Triage: Organizes thousands of alerts into the ones that really matter.
- Detailed Investigation: Tracks how an attack started, spread, and which assets were affected.
- Full-Scope Visibility: Gives a 360-degree view of your security environment.
- Prioritization: Focuses on the most dangerous threats first.
- Automation: Speeds up detection and response while reducing errors.
- Rapid Action: Responds to attacks quickly and efficiently.
- Tailored Solutions: Provides system-specific responses to reduce business impact.
Sangfor XDR: A Friendly Look at Cutting-Edge Protection
Sangfor offers a fully integrated AI-powered security ecosystem, and here are two key solutions:
Endpoint Secure (EDR) – The Always-Watching Guardian
- Provides multi-layered threat detection across endpoints and servers.
- Uses honeypots and AI engines (Engine Zero, Neural-X) for behavior analysis.
- Implements Zero Trust Micro-Segmentation to stop attackers from moving laterally.
CyberCommand – AI-Driven Command Center
- Collects traffic and logs from XDR and non-agent devices for complete coverage.
- Uses MITRE ATT&CK to correlate threats and runs automated response actions.
- Detects subtle network, user, and app anomalies with dynamic baselines.
OMNI Command Module – Smart, Real-Time Security
- Provides instant root-cause analysis powered by GPT-based AI.
- Combines endpoint, network, cloud, and asset data for high-precision detection.
- Reduces false positives below 4.3% and responds to threats in under 5 seconds.
- Automates forensic analysis and integrates with other vendor solutions.
- Performs dynamic sandbox analysis, making sure even stealthy attacks are caught.
- Keeps everything secure with on-premises deployment and offline updates.