Identity and Access Management (IAM)
What is Identity and Access Management (IAM)?
Identity and Access Management (IAM) is a framework of policies, processes, and technologies designed to ensure the right individuals have the right access to the right resources, at the right time, and for the right reasons. IAM combines identity (who a user is) and access (what they are allowed to do).
Think of IAM as the traffic controller of your organization’s digital environment:
Identifies users (human or machine)
Authenticates them (verifies their identity)
Authorizes actions based on roles and permissions
Tracks and manages user activities
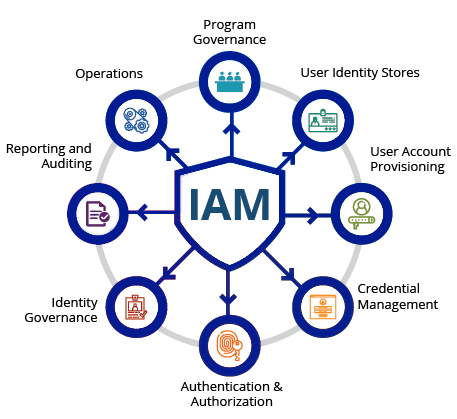
Core Functions of IAM
IAM systems provide a wide range of capabilities to manage digital identities securely and efficiently. Key functions include:
1. Identity Creation and Management
Provisioning new accounts for employees, partners, customers, or applications
Assigning attributes such as username, department, and role
2. Authentication
Verifying a user’s identity before granting access
Methods include passwords, biometrics, smart cards, OTPs, and Multi-Factor Authentication (MFA)
3. Authorization
Controlling what users are allowed to do based on roles or permissions
Example: HR employees can view salary data, while marketing employees cannot
4. Session Management
Tracking active logins and setting session timeouts
Preventing session hijacking and unauthorized access
5. Monitoring and Auditing
Logging access events for compliance and threat detection
Supports audits for regulations like GDPR, HIPAA, and PCI-DSS
6. Identity Lifecycle Management
Managing the entire lifecycle of user accounts: creation, updates, and deactivation
7. Integration with Other Systems
Connecting IAM to applications, cloud services, VPNs, and directories like Active Directory or LDAP
IAM Architecture
A modern IAM architecture typically includes:
Directory Services: Stores all identities (e.g., Microsoft Active Directory, LDAP)
Authentication Systems: Verifies users (e.g., Kerberos, SAML, OAuth, OpenID Connect)
Access Control Engines: Enforce policies and permissions
Self-Service Portals: Allow users to reset passwords, request access, and update profiles
APIs & Connectors: Integrate IAM with cloud, SaaS, and on-premise applications
Key IAM Technologies
Single Sign-On (SSO): One login for multiple applications
Multi-Factor Authentication (MFA): Combines two or more verification methods
Role-Based Access Control (RBAC): Access based on job roles
Attribute-Based Access Control (ABAC): Access based on attributes like department, time, or location
Federated Identity Management: Enables identity sharing across organizations (e.g., Google login)
Privileged Access Management (PAM): Special controls for high-level admin accounts
Benefits of IAM
Implementing IAM offers multiple advantages:
Enhanced Security: Reduces risk of unauthorized access
Regulatory Compliance: Meets legal and industry standards
Improved Productivity: Streamlines user access and reduces IT workload
Better User Experience: SSO and self-service features minimize login fatigue
Centralized Control: Manage all accounts and permissions from a single platform
Challenges of IAM
Organizations may face challenges when implementing IAM:
Complex integration with legacy systems
Balancing security with user convenience
Managing identities for a growing number of cloud applications
Continuous monitoring for compromised credentials
Popular IAM Solutions
Some widely used IAM solutions include:
Microsoft Entra ID (formerly Azure AD)
Okta
Ping Identity
CyberArk (for PAM)
IBM Security Verify
SailPoint
ForgeRock
IAM Services
IAM is a strategic tool for managing security risks, improving productivity, and ensuring compliance. With rising cyber threats, organizations are prioritizing IAM solutions to protect sensitive data and streamline user access management.
IAM Services Offered:
Identity Creation and Management
Authentication
Authorization
Session Management
Monitoring and Auditing
Identity Lifecycle Management
Integration with Other Systems
This version is structured for SEO, uses clear headings, includes keywords like IAM, identity management, access control, MFA, RBAC, and is easy to read for both humans and search engines.
If you want, I can also create a meta title, meta description, and SEO-friendly URL suggestions for this article so it’s fully optimized for Google.